
THREE BIG BACKUP AND DISASTER RECOVERY THEMES EMERGED – AND WE’VE GOT ANSWERS!
This blog post has been updated in May 2022 to provide greater information by expanding upon previous answers and include a reference to our 30-day, risk-free Veeam trial offer for you. In November 2020, Virtual Systems cohosted a live event with Veeam titled “The Biggest v11 Sneak Peek Event, Ever.” We decided to give the event an “anti-webinar feel” as an alternative to virtual presentations where attendees join, half-listen to a presenter, and maybe multitask or doze off during it. Feedback from our anti-webinar was terrific and the event was a success! We had about 450 professionals registered and, to incentivize participation, we gave away huge prizes (like thousands of dollars and next-gen gaming consoles) for good questions. This clearly worked as attendees asked over 325 questions, thereby making it the most interactive event of the year. The backup and disaster recovery questions asked helped shed some light on what IT professionals are struggling with when it comes to business continuity. And within all those questions, we discovered three major themes:1. WHAT ARE THE BASIC BUILDING BLOCKS OF GOOD ENTERPRISE BACKUP SOLUTIONS?
It’s common for IT staff to inherit someone else’s data backup & recovery project and not be familiar with it. This can create some real business continuity challenges. So, here’s a quick primer on the building blocks of backup architecture: Picture your data needs stretching across a priority continuum. On one end, you have “hot” data that is copied in shorter retention periods but is readily available for spin up in another location. On the other, colder side of the spectrum, data is stored or archived for longer retention periods. The tradeoff for those long retention periods is that live recovery of the application is slower (even though file recovery is still fast).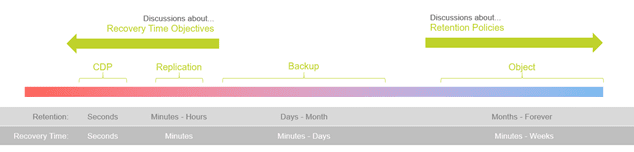 It may also be helpful to think about the way you deploy your backup solution as being kind of like how students advance through college courses:
It may also be helpful to think about the way you deploy your backup solution as being kind of like how students advance through college courses:
- Level 101 is backup, which includes applying the 3-2-1 rule (make three copies on two different types of storage and get one copy offsite).
- Level 201 is implementing replication, or hot standby for your important VM’s to recover quickly. Then develop retention policies and decide how long you need to keep different data volumes.
- Your Master’s classes give you the ability to fine-tune and take advantage of additional features, like using your backup data to create testing sandboxes.
VEEAM BACKUP & REPLICATION™
Cloud backup as a service is simple to deploy, with recovery time objectives (RTOs) and recovery point objectives (RPOs) based on your business’s needs and budget. And the best cloud backup option for any sized business is implementing Veeam backup solutions through a trusted cloud service provider like Virtual Systems. Want a risk-free way to try this out? We offer a 30-day Veeam free trial that doesn’t require you to hand over a credit card number! Veeam Backup & Replication™ jobs can run either manually or automatically per a schedule. Each job has configuration values that define what, when, how, and where to back up. Your first backup job creates a full image of each VM, and subsequent jobs only move data blocks that have been changed from the previous image. Veeam utilizes full end-to-end encryption for maximum data security and offers you complete visibility and control. You can set your backups to maximize recovery of critical data first and match your company’s retention policies for data that needs to be maintained but not regularly accessed. If you’d like to know more about how to create a Veeam backup copy job our team is happy to help you understand.2. HOW CAN YOU PROTECT DATA FROM RANSOMWARE?
Another major theme from the questions IT professionals often have is protecting data from a ransomware attack. This is particularly relevant because attacks are occurring more frequently and taking a bigger toll. Veeam reports that 93 percent of organizations are attacked every year. The best answer we can give you to address potential data loss to ransomware is to prepare for the worst. In other words: don’t prepare for “if” it will happen, prepare for “when.” RELATED: Why Customer Data Protection Should Be at the Top of Your Priority ListBEST PRACTICES AGAINST RANSOMWARE IN DATA BACKUP AND RECOVERY
A big part of preparation is practicing in a controlled environment. Once you’ve got backup jobs and replicas running offsite, conduct an event where your primary site goes down. Practice rolling back your environment to the moment before ransomware may have been delivered. If this is intimidating, leverage our team. We walk our customers through this process every week and it doesn’t cost a thing, and when a malicious event occurs this experience is invaluable. When you’re confident in your BDR solution, you prevent missteps due to panic at a time when good decision-making is critical. Other best practices include:- Offline, encrypted data backups of critical data. Malicious parties can’t hold for ransom data that they have no access to.
- Create a disaster response plan and disseminate to all appropriate parties. Ensure that responsibilities are clear so that each person knows how to react to a cyberattack.
- Remote devices are often the source of vulnerabilities. Secure your remote work – or partner with a cloud service that specializes in remote security – to reduce attack vectors.
- Phishing is another huge vulnerability, which can be resolved through cybersecurity training and end-user reporting of suspicious incidents.
3. CAN I BACK UP LINUX?
Although we had numerous questions about backing up Microsoft365, Windows and Mac, there’s a high number of businesses using Linux systems due to the flexible nature of the open-source OS. Linux can save large organizations thousands of dollars in licensing fees and reduce their reliance on a commercial platform with proprietary code. Veeam supports Linux-specific features, including a Linux file restore feature that doesn’t require a helper appliance and a hardened Linux repository with a landing zone that you can configure to be malware-proof and set policies that make data immutable (aka unchangeable). Also, you can reassure your users that immutability isn’t exclusive to Linux backups. You can set flags that make any data at rest immutable so that even a cloud provider couldn’t delete it. Veeam backup for Linux is simply a matter of using the built-in tool in Veeam Backup and Replication – the Veeam Agent for Linux. With automatic deployment of Veeam Agents, this isn’t a machine-by-machine task, all data protection and disaster recovery tasks can be deployed remotely from the Backup and Replication dashboard. Many people think Linux is more challenging to use, but it doesn’t have to be. Sometimes you just need the right tools for the job.SO MANY BACKUP AND RECOVERY QUESTIONS, SO LITTLE TIME
The idea of building a short-lived, mini community inside of our 2020 live event proved a huge success. While we couldn’t answer all 325+ questions participants had during the anti-webinar, our team is always here to answer your individual questions. If something’s on your mind, let us know by contacting us here. Enterprise backup solutions are clearly a hot topic among sysadmins, and Veeam backup software can really ease the process for creating actual functional disaster recovery controls. If you’ve got two minutes, we dig into backups vs. replicas as a recovery solution on our YouTube channel. Check it out and tell us what you think!Share
Resources + Updates